BLOG
Breaking Up Is Hard to Do
Change is never easy, even if you’re getting out of a relationship that’s no longer working for you. We know this from experience. Nearly every time we bring on a new client, they’ve recently broken up with their old IT firm or had employees quit or get fired. ...
It’s the People, Stupid
Have you ever heard the technology acronym PEBKAC? Or maybe PICNIC or an ID-10T error? If not, I’ll let you in on this secret IT slang: PEBKAC - "Problem Exists Between Keyboard And Chair” PICNIC - "Problem In Chair Not In Computer" ID-10T error - "Idiot error" Funny...
The End of The Life Of The Windows 2012 R2 Server
On October 31, 2023, Windows 2012 R2 Server will reach its end of life. Microsoft will cease all support of this product, including security updates. Continuing to use it after the deadline will put your business at risk. If you don’t know if your company is currently...
Data Encryption: Best Practices for Business Owners
Waident’s cybersecurity philosophy is simple: Hackers hack easy targets, so the more layers of security an organization puts in place the harder the effort to penetrate and the less attractive a target it becomes. Encryption is one of those important layers. It is a...
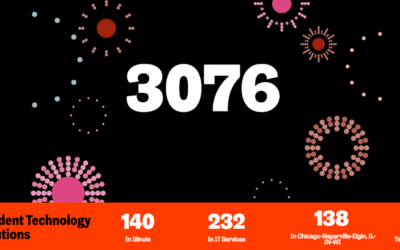
Waident Recognized on the INC. 5000™ List of Fastest Growing Companies
We are announcing a major milestone in our journey – being recognized as the #3076 company on the prestigious INC. 5000™ list. This achievement is a testament to the dedication and hard work of our incredible team and our valued customers' unwavering support. As we...
The Importance of Data Classification in Your Cybersecurity
In my last post, I covered the important topic of Data Access — determining who, why, and when to use data sources. In this blog post, I dig into Data Classification, which designates the “what” of data, and explore best practices I recommend to our clients. What is...
Curious Tech – August
Hey there, tech enthusiasts, get ready to be impressed by Curious Tech! Summer is still here, you can use a few of those items. Anti-flies fan BBQ season is still here! Annoyed by flies checking...
Waident Successfully Completes AICPA SOC 2 Examination
I am pleased to announce that Waident successfully completed its SOC 2® (System and Organization Control 2) examination and received a report dated May 31, 2023. SOC 2 is an important framework for assessing and reporting on the security, availability, processing...
Best Practices for Managing Data Access
Information powers your organization. It identifies trends, helps you serve customers, enables smarter decisions, fulfills compliance obligations, and fuels innovation. It can also put your company at risk. Waident held a cybersecurity event several years ago. The...
Oh, Sh*t! You Seriously Mean to Tell Me That I Could Lose All of My Cloud Data?
Most of us would probably agree that the cloud has turned out to be a boon for business computing. But, have we grown too confident in “the cloud” and now putting too much faith in the cloud systems we are using? Do you assume that your data is secure and that data...
The Pitfalls of Unwisely Retiring Old Office Technology
Pursuing sustainability is a noble goal and more and more environmentally conscious businesses are rising to the challenge. A common example is upgrading and then reselling old technology like routers, firewalls, and switches to others who extract more life out of...
Curious Tech – May
And it’s already May! Some ideas on how to impress your friends and family. Here is my May curious tech list: Giant Spider Pillow It is kind of creepy having a huge fuzzy spider pillow, but it is kind of cool....
Subscribe
Get our latest tools and thinking.